Cyber operations as legitimate collective countermeasures in the current armed conflict in Ukraine: an international law perspective

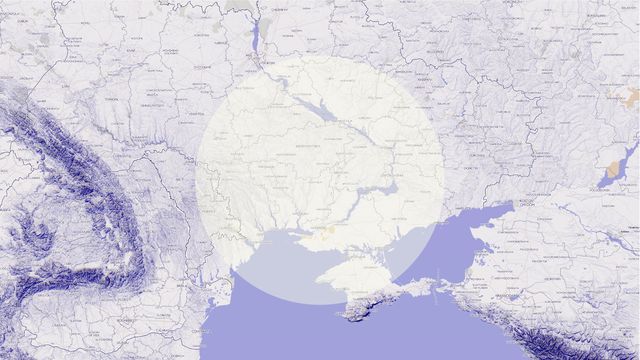
Since the beginning of the armed conflict in Ukraine, there has been an escalation of (state-sponsored) cyber-operations targeting both Ukrainian and Russian networks.
In particular, we see more and more (state-sponsored) hackers who are siding with Ukraine and claiming cyber-operations targeting Russian websites. Two cases worth mentioning are Ukraine's "IT army" - volunteer hacking forces that have been called upon by representatives of the Ukrainian government to join forces against Russian networks - and Anonymous - who declared on Twitter to be “in cyber war” against Russia. Additionally, a number of European countries (like Lithuania, Netherlands, Poland, Estonia, Romania and Croatia) are giving technical support to Ukraine under the initiative of the European Union’s Cyber Rapid Response Teams in order to efficiently address cyber-attacks.
In peaceful times, these kinds of cyber-operations might trigger the responsibility of states, to the extent that cyber-operations “constitute […] a breach of an international legal obligation”, i.e. when they “violate the sovereignty of another State” or when they “intervene in the internal or external affairs of another State”.
In the current circumstances, cyber-operations carried on by or in support of Ukraine against Russian networks can instead be considered as legitimate forms of (collective) countermeasures. In this respect, the following should be taken into consideration:
Russia has breached its international obligations
Military and cyber-operations undertaken by Russia towards Ukraine are in breach of several norms of international law, including Russia’s violation of the prohibition of the use of force.
Cyber-operations carried on by Ukraine are lawful means of countermeasures
As targeted state, Ukraine is entitled to respond with countermeasures towards a prior internationally wrongful act of Russia, until the act has not ceased.
Generally, countermeasures should not necessarily be of the same nature as the wrongful acts to which they are responding. The main aim of countermeasures is to induce the responsible State to cease violations of international law. Countermeasures should be terminated when the responsible State has complied with its international obligations. Also, they should be terminated when “the dispute is pending before a court or tribunal”. However, if the State “is not cooperating in that process […] or fails to appear before the tribunal once it is established”, countermeasures can legitimately continue. Thus, until Russia refuses to appear before the International Court of Justice, Ukraine is entitled to adopt countermeasures.
States can assist Ukraine in conducting collective cyber countermeasures
There is an ongoing debate whether one State may assist another in conducting cyber countermeasures, or even conduct the countermeasures on its behalf. Under international law, third non-injured States may take action towards the responsible State in order to induce compliance with international obligations that are owed to the international community, such as the prohibition of aggression.
When it comes to cyberspace, Estonia has been so far the only state that has expressed it very clearly that third states “may apply countermeasures to support the state directly affected by the malicious cyber operation”, a view that has found also some support in scholarship. Today, this seems to be supported by the practice of several states that are siding with Ukraine and providing technical cyber-support. In this scenario, collective cyber-measures can be considerate legitimate under international law.
Cyber-operations carried on by Anonymous or private groups or individuals against Russia can(not) be considered as forms of countermeasures
As recalled by the Tallinn Manual 2.0 on the International Law Applicable to Cyber Operations, “[o]nly […] State may engage in countermeasures”.
So, what about cyber-operations carried out by Ukraine's "IT army” and Anonymous?
As regards Ukraine's "IT army”, it seems that it receives instructions from Ukrainian government representatives through the group`s Telegram channel. Accordingly, they can qualify as a private group “acting on the instructions of […]” Ukraine, i.e. on its behalf. Therefore, the cyber-operations they carry on can be considered as forms of countermeasures carried out by Ukraine.
Instead, when it comes to Anonymous, there is no evidence that they are acting under the instructions of Ukraine/any other state; rather, they act as private individuals. As such, they are subject to the relevant national jurisdictions (and the applicable national (cyber-criminal) laws). However, in case of “cyber operations related to an armed conflict, their activities [… should comply with] the law of armed conflict”, even though international law does not specify how to identify those cyber-operations that are carried on by individuals “in the context of and associated with the armed conflict”.